By: Danstan Akwiri
Introduction:
In today’s interconnected digital landscape, the presence of malware poses a significant risk to individuals, businesses, and organizations. Malware, a term encompassing various malicious software, can infiltrate systems, compromise data, disrupt operations, and gain unauthorized access. To ensure the safety of our digital lives, it is crucial to understand the different types of malware, their potential impacts, and implement effective preventive measures.
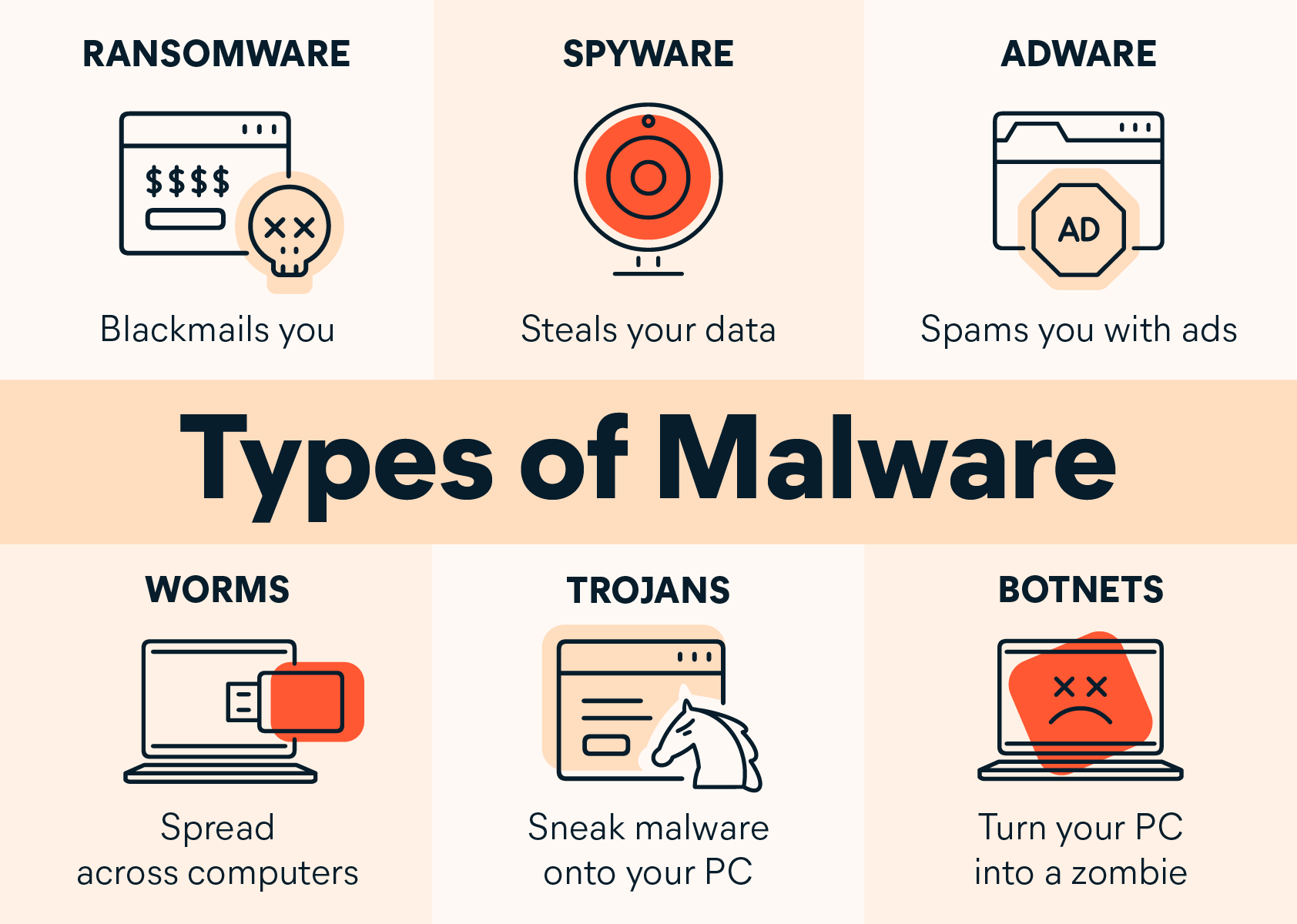
Types of Malware:
- Viruses: Viruses attach themselves to files and spread when those files are executed, often causing damage or unauthorized actions.
- Worms: Worms self-replicate and spread across networks, consuming system resources and potentially disrupting operations.
- Trojans: Trojans masquerade as legitimate software, tricking users into executing them. They often create backdoors for attackers or steal sensitive information.
- Ransomware: Ransomware encrypts files, rendering them inaccessible until a ransom is paid. This type of malware has seen a significant rise, targeting individuals and organizations alike.
- Spyware: Spyware silently monitors user activities, capturing sensitive information such as passwords, financial data, or browsing habits.
- Adware: Adware displays unwanted advertisements, often bundled with legitimate software installations. It can track user behavior and compromise privacy.
Impacts of Malware: Malware can have severe consequences, including:
- Data Breaches: Malware can exfiltrate sensitive data, leading to identity theft, financial loss, or reputation damage.
- Disruption of Operations: Certain malware, such as worms or denial-of-service (DoS) attacks, can render systems or networks inaccessible, resulting in downtime and financial losses.
- Financial Fraud: Malware targeting online banking or payment systems can facilitate fraudulent transactions, causing substantial monetary harm.
- Loss of Privacy: Spyware and adware compromise personal privacy, monitoring online activities and collecting sensitive information.
Mitigating Malware Risks:
- Use Antivirus Software: Install reputable antivirus software and keep it up to date. Regularly scan your system to detect and remove malware.
- Regular Updates: Ensure operating systems, software, and applications are updated with the latest security patches to address known vulnerabilities.
- Exercise Caution Online: Be cautious when opening email attachments, downloading files, or visiting unfamiliar websites. Avoid clicking on suspicious links or ads.
- Enable Firewalls: Activate firewalls on your devices and networks to filter incoming and outgoing traffic, providing an additional layer of protection.
- Backup Important Data: Regularly back up your critical files and data to an external storage device or cloud service to mitigate the impact of potential ransomware attacks.
- Educate Users: Promote cybersecurity awareness among individuals and employees. Teach them about phishing, social engineering, and safe online practices to reduce the risk of malware infections.
In summary the face of increasing malware threats, understanding the various types of malware and their potential impacts is essential. By implementing proactive measures such as using antivirus software, keeping systems updated, exercising caution online, enabling firewalls, and educating users about safe practices, we can significantly mitigate the risks associated with malware. Stay vigilant, prioritize cybersecurity, and adopt best practices to protect your digital world from the pervasive threats of malware.
Danstan Akwiri, (Master’s Degree in Computer Science)
Cybersecurity Analyst.
Head of Cybersecurity Division (Cyberpro Africa).
CCNA certifies.
Similar Posts by Mt Kenya Times:
- Mau Mau descendants push for recognition and compensation at Thika conference
- NEWS IN BRIEF 13 MAY 2026
- Exodus in Murang’a: 18 former MCAs join Safina in major political realignment
- Mt Kenya Times ePAPER May 13, 2026
- Democratic Party of Kenya strengthens global women leadership ties at Morocco conference